Windows Kernel: Vulnerability Hunting Training
Windows Kernel: Vulnerability Hunting Training
Instructor of the training: Juan Sacco is a security researcher and exploit developer specialising in reverse engineering, exploit development, and Windows kernel exploitation. He is the founder of Exploit Pack. [LinkedIn] [GitHub]
This training provides a deep, practical introduction to Windows kernel vulnerability hunting. By the end of the course, you’ll understand the full workflow, from identifying vulnerable drivers to reversing and classifying vulnerabilities using industry-standard tools.
What You Will Learn
- PE structure and Windows internals
- Driver internals, architecture, and debugging
- Set up a proper lab environment for driver vulnerability research
- Fuzzing Windows drivers using external tools
- Ghidra and IDA Pro: from zero knowledge to reversing real samples
- Using plugins for enhanced decompilation and reverse engineering
- Analyse samples and understand vulnerability classes and types
- Exploitation fundamentals and classification
Windows 11 security protections relevant to vulnerability hunting, including:
- KASLR
- Shadow Stack
- SEH
- SMEP/SMAP
- Hypervisor-based protections (VBS / HVCI)
Course Overview
You’ll learn where and how to find real-world samples, how to identify vulnerabilities in Windows drivers, and how to dissect them by classification and type. We’ll slowly walk you through reversing these issues using Ghidra and IDA Pro, supported by dedicated plugins and tooling.
Topics Covered
- Using IDA Pro and Ghidra for vulnerability research
- Reversing PE binaries and WDM drivers
- Exploit types and classification
- Windows 11 exploit mitigations
- Understanding and bypassing driver-level protections
- Filtering, protection, and obfuscation techniques used by software vendors, including IOCTL hiding
Hands-on Exercises & Materials
You will practice against real vulnerable drivers and examples, including:
- Instructor-built drivers and applications
- Real-world vendor PoCs and samples
Tools & Resources Provided
Participants receive access to a set of tools used during the course:
- IOCTL++
- DriversHunter app for the Windows Catalogue
- IDA and Ghidra debugging plugins
- GUI for IOCTL Lance
- Additional tooling, scripts, and supporting materials
Format & Delivery
- Format: Pre-recorded videos (learn at your own pace)
- Content: 4 video modules + downloadable tools and materials
- Practical exercises: Included
Support & Community
Participants can join our Discord channel #training, where they can share progress, ask questions and collaborate with instructors and other learners
Couldn't load pickup availability



You may also like..
-
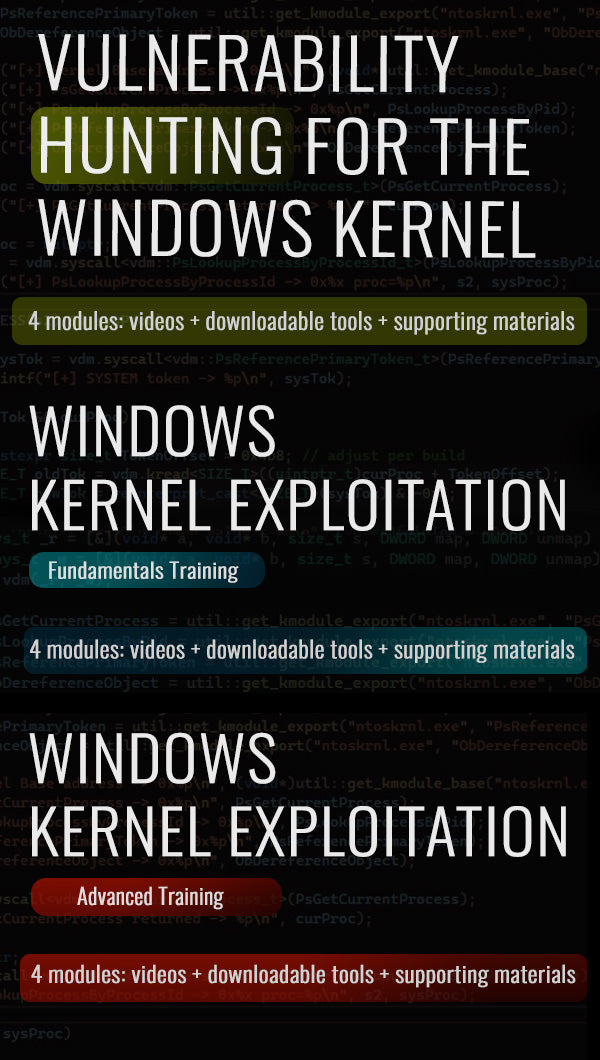
Windows Kernel Exploitation [Fundamentals]
Regular price From €600 EURRegular priceEURSale price From €600 EUR -
Windows Kernel: Vulnerability Hunting Training
Regular price From €600 EURRegular priceEURSale price From €600 EUR -
Windows Kernel Exploitation [Advanced]
Regular price From €600 EURRegular priceEURSale price From €600 EUR


![Windows Kernel Exploitation [Fundamentals]](http://www.exploitpack.com/cdn/shop/files/TrainingFundamentals.jpg?v=1777829306&width=533)

![Windows Kernel Exploitation [Advanced]](http://www.exploitpack.com/cdn/shop/files/TrainingAdvanced.jpg?v=1777829406&width=533)